热力环流是大气运动最简单的一种形式。读图,完成下列各题。(10分)
(1)热力环流是由地面 不均形成的。
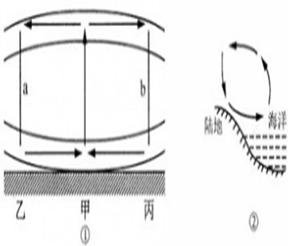
(2)图①中,甲地近地面气压 (低于或高于)乙地。甲乙之间的大气水平运动就是风。 是形成风的直接原因。因为 力使风向发生偏转,北半球向
(左或右)偏。在近地面,风向与等压线 (平行或斜交)
(3)请在图①中a、b线段上分别补画箭头,完成甲—乙和甲—丙之间的热力环流。
(4)图②所示的海陆热力环流现象通常出现在 (白天或夜间)。
(5)图中乙地夜间天气晴朗,则在初冬的清晨上学时人们会发现地上“下霜了”,请从地理角度解释一下这个现象: 。