(12分)有机高分子化合物甲是
一种常用的光敏高分子材料,其结构简式为: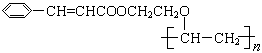 。
。
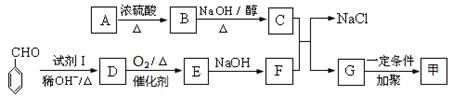
按图可以合成甲,其中试剂Ⅰ可由相对分子质量为26的烃与水加成制得。
已知:
①-CH2OH + -CH2OH  -CH2OCH2- + H2O
-CH2OCH2- + H2O
②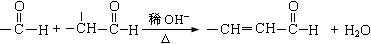
回答下列问题:
(1)试剂Ⅰ的名称是 ;B→C的反应类型是 ;
(2)质谱图显示A的相对分子质量是80.5;A分子中氧元素的质量分数为19.88%,碳元素的质量分数为29.81%,其余为氢元素和氯元素,且A的核磁共振氢谱上有三个吸收峰,峰面积的比例为2:2:1,则A的结构简式为 。
(3)写出下列反应的化学方程式。
①D→E的反应 ;
②C与F的反应 。
(4)E的一种同分异构体,水解产物有两种,一种能使溴水褪色,另一种在滴加饱和溴水后,有白色沉淀生成,该物质的结构简式为 。
(1)乙醛 消去反应
(2)ClCH2CH2OH
(3)① 2  -CH="CHCHO" + O2
-CH="CHCHO" + O2  2
2  -CH=CHCOOH
-CH=CHCOOH
② -CH=" CHCOONa" + ClCH2CH2OCH= CH2 →
-CH=" CHCOONa" + ClCH2CH2OCH= CH2 →
 -CH= CHCOOCH2CH2OCH= CH2 + NaCl
-CH= CHCOOCH2CH2OCH= CH2 + NaCl
(4) -OOCCH=CH2
-OOCCH=CH2
(1)试剂Ⅰ的名称是乙醛;B→C的反应类型是消去反应
(2)由已知条件可推知A 的分子式为:C2H5OCl,又因为A的核磁共振氢谱上有三个吸收峰,峰面积的比例为2:2:1,则A的结构简式为ClCH2CH2OH
(3)①D→E的反应:2  -CH="CHCHO" + O2
-CH="CHCHO" + O2  2
2  -CH=CHCOOH
-CH=CHCOOH
②C与F的反应: -CH= CHCOOCH2CH2OCH= CH2 + NaCl
-CH= CHCOOCH2CH2OCH= CH2 + NaCl
(4)E的一种同分异构体能发生水解,应是一种脂类物质,能使溴水褪色,说明有碳碳双键,滴加饱和溴水后,有白色沉淀生成,说明存在酚类物质,所以,该物质的结构简式为 -OOCCH=CH2
-OOCCH=CH2
