Clattering keyboards may seem the white noise of the modern age, but they betray more information than unwary typists realize. Simply by analyzing audio recordings of keyboard clatter, computer scientists can now reconstruct an accurate transcript of what was typed--including passwords. (41) .
Such snooping is possible because each key produces a characteristic dick, shaped by its position on the keyboard, the vigor and hand position of the typist, and the type of keyboard used. But past attempts to decipher keyboard sounds were only modestly successful, requiring a training session in which the computer matched a known transcript to an audio recording of each key being struck. (42) . Furthermore, each new typist or keyboard required a fresh transcript and training session, limiting the method’s appeal to would-be hackers.
Now, in a blow to acoustic security, Doug Tygar and his colleagues at the University of California, Berkeley, have published details of an approach that reaches 96% accuracy, even without a labeled training transcript. (43) . The software tentatively assigns each click a letter based on its frequency, then tests the message created by this assignment using statistical models of the English language. For example, certain letters or words are more likely to occur together-if an unknown keystroke follows a "t", it is much more likely to be an "h" than an "x". Similarly, the words "for example" make likelier bedfellows than "fur example". In a final refinement, the researchers employed a method many students would do well to deploy on term papers., automated spellchecking.
By repeatedly revising unlikely or incorrect letter assignments, Dr. Tygar’s software extracts sense from sonic chaos. That said, the method does have one limitation: in order to apply the language model, at least five minutes of the recorded typing had to be in standard English (though in principle any systematic language or alphabet would work). But once those requirements are met, the program can decode anything from epic prose to randomized, ten-character passwords.
(44) . He says it is quite simple to find the instructions needed to build a parabolic or laser microphone on the web. You could just point one from outside through an office window to make a recording. And as he points out, would-be eavesdroppers might not even need their own recording equipment, as laptop computers increasingly come equipped with built-in microphones that could be hijacked.
(45) . His computers were less successful at parsing recordings made in noisy rooms. Ultimately, though, more sophisticated recording arrays could overcome even background noise, rendering any typed text vulnerable. Dr. Tygar therefore recommends that typed passwords be phased out, to be replaced with biometric checks or multiple types of authorization that combine a password with some form of silent verification (clicking on a pre-chosen picture in a selection of images, for example). Loose lips may still sink ships, but for the moment it seems that an indiscreet keystroke can do just as much damage.
[A] This sort of acoustic analysis might sound like the exclusive province of spies and spooks, but according to Dr. Tygar, such attacks are not as esoteric as you might expect.
[B] The sounds of typing can be decoded, which can be used to decode password, so if you are typing random, secure passwords.
[C] The new approach employs methods developed for speech-recognition software to group together all the similar-sounding keystrokes in a recording, generating an alphabet of clicks.
[D] To protect against these sonic incursions, Dr. Tygar suggests a simple remedy: turn up the radio.
[E] The major advance here is that it no longer requires hours of training the model in order to create a usable mapping of key sounds to letters.
[F] And in contrast to many types of computer espionage, the process is simple, requiring only a cheap microphone and a desktop computer.
[G] Thus schooled, the software could still identify only 80% of the characters in a different transcript of the same typist on the same machine.
 ,内阻忽略不计.闭合开关
,内阻忽略不计.闭合开关 ,电灯正常发光。再将滑动变阻器的滑片
,电灯正常发光。再将滑动变阻器的滑片 稍向左移动一段距离,下列说法正确的是
稍向左移动一段距离,下列说法正确的是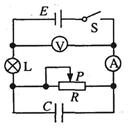
 ,
, 不变,则灯泡变暗,故B正确.
不变,则灯泡变暗,故B正确. ,电源的功率减小,C错误.
,电源的功率减小,C错误.